Demystifying the Technical Documentation Required by the Cyber Resilience Act
The European Union’s Cyber Resilience Act (CRA) will reshape the landscape of cybersecurity for connected devices.
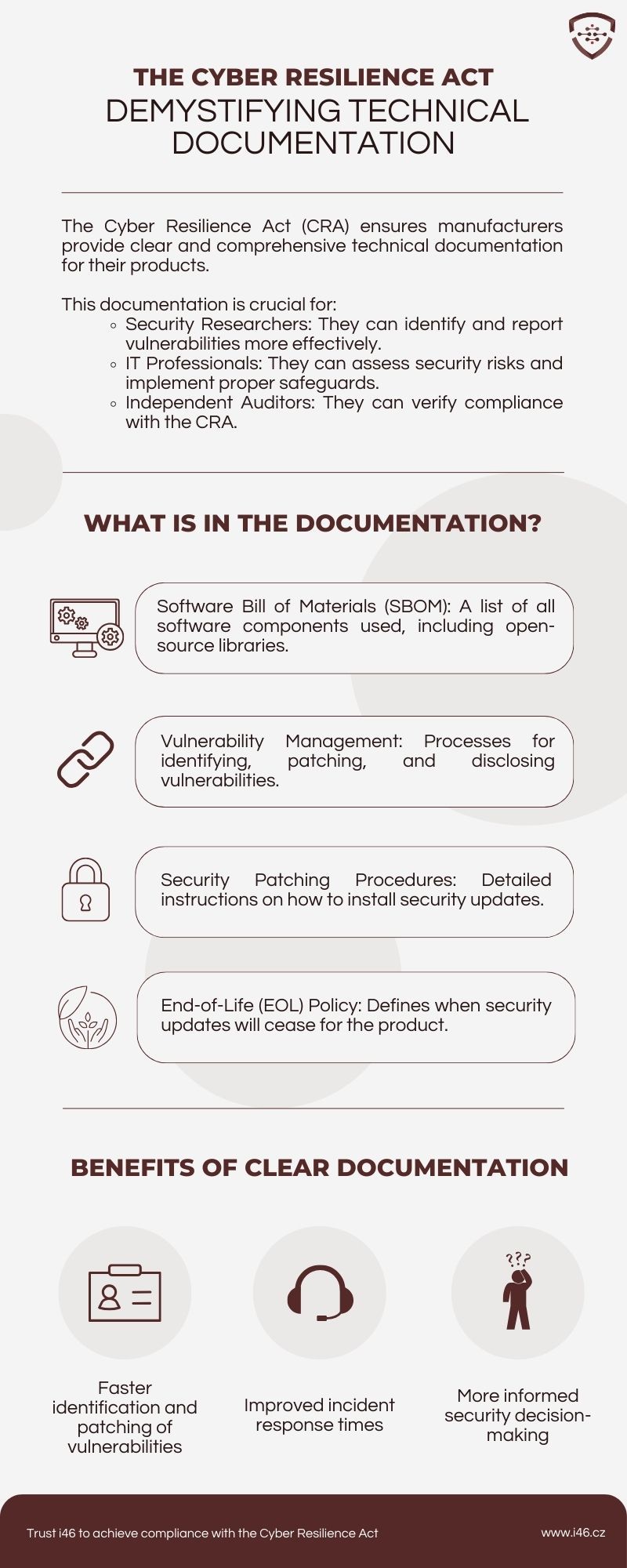
This new regulation mandates that manufacturers provide clear and comprehensive technical documentation for their products. But what exactly does this documentation entail, and why is it so crucial for achieving compliance with the CRA?
This article will help you demystify the the Technical Documentation required by the Cyber Resilience Act
What Should the Documentation Include?
The above infographic outlines some of the key elements that should be included in technical documentation to ensure CRA compliance:
- Software Bill of Materials (SBOM): A detailed list of all software components used in the product, including open-source libraries. This transparency enables a more holistic understanding of the product’s security posture.
- Vulnerability Management: Clear processes for identifying, patching, and disclosing vulnerabilities throughout the product lifecycle. This proactive approach is essential for mitigating cyber threats and protecting user data.
- Security Patching Procedures: Step-by-step instructions on how to install security updates for the device. User-friendly patching procedures are crucial for ensuring that devices remain secure and protected against known vulnerabilities.
- End-of-Life (EOL) Policy: A clear definition of when security updates will cease to be provided for the product. This information allows users to make informed decisions about the continued use of a device after its official support period has ended.
Where should the Documentation be provided?
Manufacturers of IoT products and software will have to provide the Technical Documentation to their customers.
This can be done in several forms:
- Printed Documentation: This is a requirement for manufacturers of physical IoT products. These stakeholders will have to ship the products with the technical documentation included in the product’s packaging.
- Electronic form: For developers of software products targeted by the CRA, but also for manufacturers of IoT products, an other way to provide product users with the Technical Documentation for their products is through an online page publicly accessible. In that case, the product users must be provided with the page URL of their product documentation after purchasing the software or IoT product.
The Power of Documentation
Here, it bears reminding that technical documentations, as required by the CRA, is an industry best practice, already being implemented by various stakeholders in the cybersecurity space:
- Security Researchers: With clear documentation, security researchers can more efficiently identify and report vulnerabilities in connected devices. This fosters a collaborative environment where vulnerabilities can be addressed swiftly, minimizing potential risks.
- IT Professionals: Comprehensive documentation empowers IT professionals to effectively assess security risks associated with specific devices. This knowledge is instrumental in implementing proper safeguards and ensuring the overall security posture of an organization’s IoT network.
- Independent Auditors: The availability of thorough technical documentation allows independent auditors to verify a manufacturer’s adherence to the CRA’s requirements. This independent verification strengthens trust and transparency within the regulatory ecosystem.
Takeaway
Clear and comprehensive technical documentation is not just a box to tick for CRA compliance; it’s a cornerstone of a robust cybersecurity strategy. By providing detailed information about their products, manufacturers can empower various stakeholders to play their part in securing the IoT ecosystem. This collaborative approach, facilitated by thorough documentation, is essential for building a future where innovation and security go hand-in-hand.
Remember, with the CRA on the horizon, prioritizing the development and maintenance of comprehensive technical documentation is no longer optional – it’s a critical step towards achieving compliance and building trust in the increasingly interconnected world of IoT devices.
Join the Discussion:
Chat with i46’s CEO: Erel Rosenberg
Find out more information on the Cyber Resilience Act here