The Cyber Resilience Act: Unpacking Risk Assessments for Secure Products
The European Union (EU) is taking a significant step towards a more secure digital landscape with the implementation of the Cyber Resilience Act (CRA). This groundbreaking legislation introduces a standardized approach to cybersecurity across the entire lifecycle of products with digital elements, from design and development to post-market support. A key pillar of the CRA is the mandatory implementation of risk assessments by manufacturers. This article delves into the essential aspects of these assessments, their role in ensuring product security, and how companies can navigate this crucial compliance requirement.
The Scope of Risk Assessments under the CRA
The CRA applies to a broad range of products, encompassing both hardware and software components that connect to the internet or have digital functionalities. This includes devices like smart TVs, medical equipment, connected toys, and a wide variety of software applications.
The legislation mandates manufacturers to conduct a comprehensive security risk assessment for all products falling under its purview. This assessment should be a thorough examination of potential cybersecurity vulnerabilities associated with the product. It should consider the product’s intended purpose, foreseeable use cases, and potential attack vectors that malicious actors might exploit.
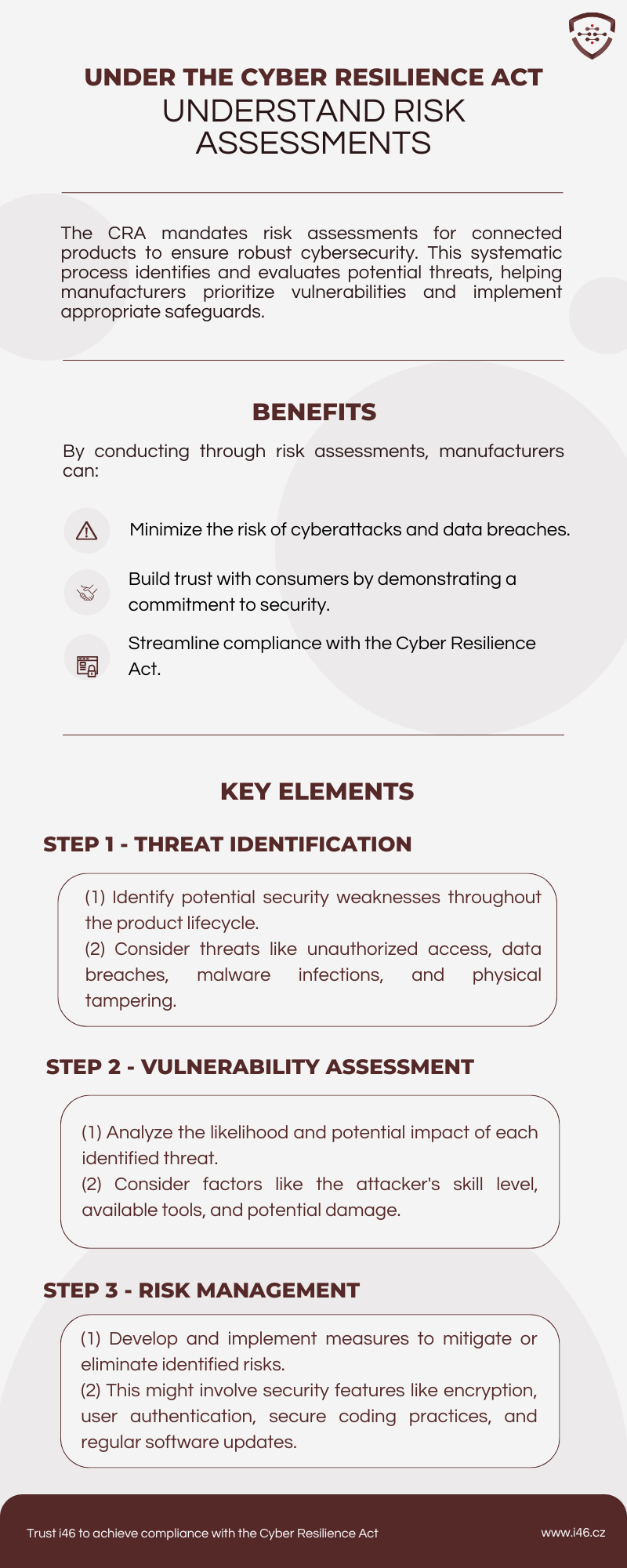
Key Components of a CRA Risk Assessment
The CRA provides a framework for conducting these risk assessments. Here are some of the key elements that manufacturers need to address:
- Threat Analysis: This involves identifying potential threats that the product could face. This includes common cyberattacks such as malware injection, data breaches, denial-of-service attacks, and unauthorized access. The assessment should consider the severity of each threat and the likelihood of it occurring.
- Vulnerability Assessment: Once threats are identified, manufacturers need to assess the product’s vulnerabilities that could be exploited by these threats. This includes examining software flaws, hardware weaknesses, and misconfigurations that could create security gaps.
- Impact Assessment: The risk assessment should also evaluate the potential impact of a successful cyberattack on the product, its users, and the broader ecosystem. This could include data loss, financial damage, reputational harm, or even physical safety risks depending on the product’s function.
- Risk Prioritization: Based on the threat analysis, vulnerability assessment, and impact assessment, manufacturers need to prioritize the identified risks. This helps them focus their efforts on mitigating the most critical vulnerabilities first.
Beyond the Basics: Essential Considerations
The CRA goes beyond a simple checklist approach to risk assessments. Here are some additional aspects manufacturers should consider:
- Secure Development Lifecycle (SDL) Integration: The risk assessment process should be integrated throughout the product development lifecycle. This ensures that security considerations are woven into the design, development, and testing phases, leading to a more robust product from the outset.
- Attack Trees: Utilizing attack trees can be a valuable tool to map out potential attack paths and their corresponding security objectives. This visual representation helps identify weaknesses and prioritize mitigation strategies.
- Essential Requirements: The CRA outlines essential requirements for secure products. The risk assessment should evaluate how well the product adheres to these requirements and identify areas where additional security measures are needed. Examples of these requirements include secure coding practices, patch management procedures, and vulnerability disclosure policies.
- Documentation and Continuous Monitoring: The findings of the risk assessment need to be documented and maintained as part of the product’s technical documentation. Additionally, risk assessments are not a one-time activity. The CRA emphasizes the importance of continuous monitoring to adapt to evolving threats and vulnerabilities. Manufacturers should regularly revisit their assessments and update them as needed.
Benefits of Comprehensive Risk Assessments
Implementing thorough risk assessments under the CRA offers numerous advantages for both manufacturers and consumers:
- Enhanced Product Security: By proactively identifying and addressing vulnerabilities, manufacturers can significantly reduce the risk of cyberattacks on their products.
- Improved Market Access: Compliance with the CRA paves the way for easier product placement across the EU market with the CE marking, signifying adherence to cybersecurity standards.
- Reduced Costs: Early detection and mitigation of security risks can save manufacturers significant resources in the long run compared to dealing with the aftermath of a cyberattack.
- Increased Consumer Trust: Consumers benefit from the peace of mind that comes with knowing the products they purchase have undergone rigorous security assessments.
Navigating the CRA: Resources and Support
The European Commission recognizes that implementing the CRA might pose challenges for some manufacturers. To assist them, the Commission is developing various resources and support mechanisms. These include:
- Guidance documents: The Commission is providing detailed guidance documents that explain the requirements of the CRA and offer practical advice for conducting risk assessments.
- Standardized methodologies: Standardized methodologies for conducting risk assessments are being developed to ensure consistency and effectiveness across industries.
- Certification bodies: Certification bodies will be available to help manufacturers assess their products and ensure compliance with the CRA.
Conclusion: A Collaborative Effort for a Secure Future
The Cyber Resilience Act marks a significant step towards a more secure digital landscape. By mandating risk assessments, the CRA empowers manufacturers to proactively identify and address security weaknesses throughout a product’s lifecycle. This not only protects consumers but also fosters a culture of security awareness within organizations and strengthens the overall digital infrastructure. The success of this initiative hinges on a collaborative effort between manufacturers, regulators, and consumers. By working together, stakeholders can leverage the power of risk assessments to build a more secure and resilient digital future for all.